The internet relies heavily on server infrastructure to deliver the websites, videos, and audio files we consume daily. These servers can be used for personal file hosting or service delivery in the enterprise. In some cases, you may wish to add a middle-man server into the equation to protect your web hosting infrastructure, or anonymise your network traffic. This middleman is called a proxy server.
What is a proxy server?
Also known as a forward proxy, a proxy server sits between the hosting server and the connected client device. When the client device wants to connect to your hosting server, it queries the proxy server first. The proxy server then connects to your hosting server, pulls the requested data, and delivers it back to the client device.
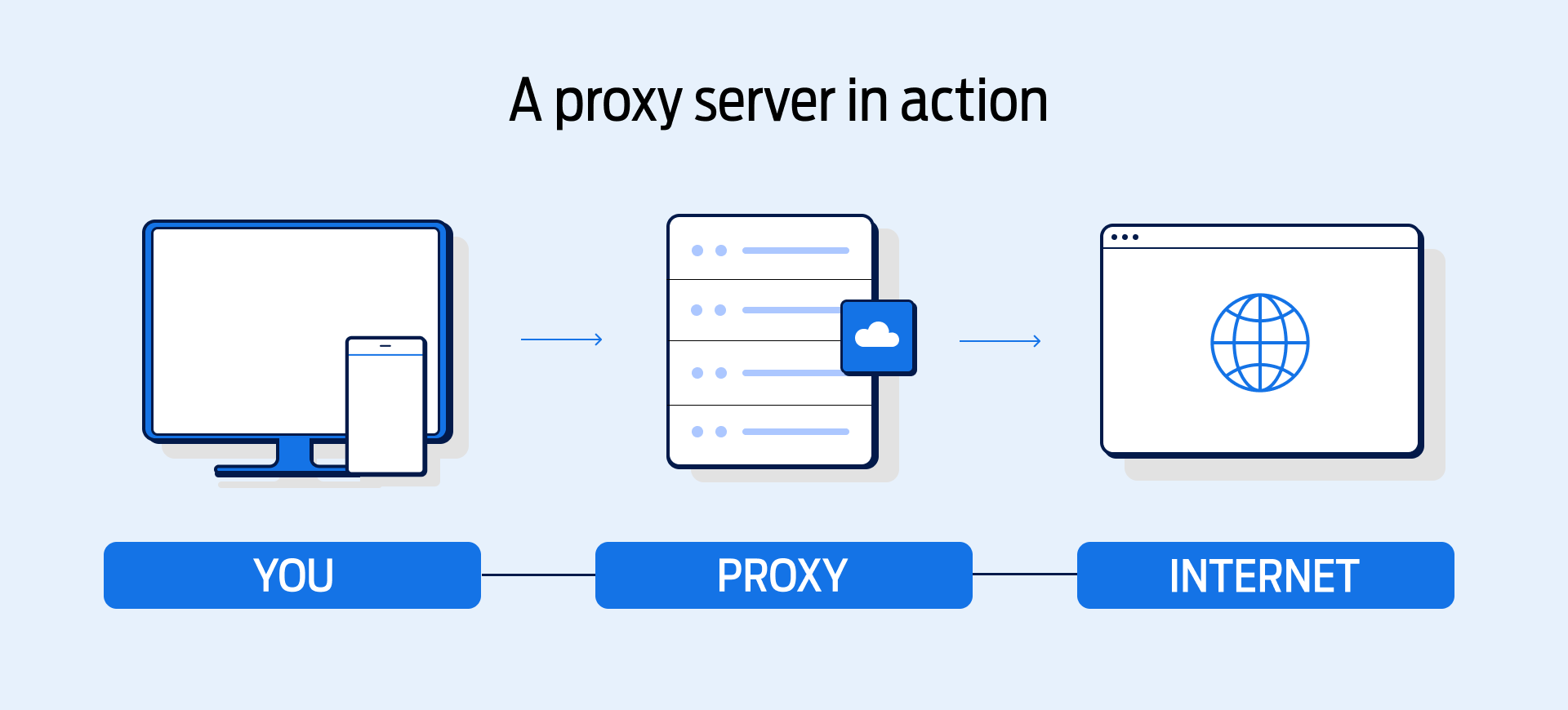
You can see a visualisation of the typical proxy data flow below and in the diagram above:
Client Device -> Proxy Server -> Hosting Server -> Proxy Server -> Client Device
How does a proxy server work?
The client device uses your proxy server domain name system (DNS) service instead of the one from the clients' internet service provider (ISP). This can help client devices to bypass geo-restricted content filters from their ISP and even helps to anonymise and secure network traffic. This anonymity is achieved when the proxy server encrypts network traffic in-transit, preventing your ISP from viewing data packet information. Since the proxy server encrypts data packets before forwarding them, your ISP cannot decipher the network protocol being used, thus preventing any throttling or filtering.
Are proxy servers useful?
For IT engineers managing hosting infrastructure, a proxy server can be incredibly useful for troubleshooting. Your ISP's DNS cache is usually cleared and refreshed every 72 hours. That means three days of latency for any new DNS records that appear in the meantime. This can cause an error message like ERR_NAME_NOT_RESOLVED to appear in your browser, despite the website being live in reality. By routing traffic through a proxy server, you use the proxies ISP connection rather than your own, eliminating these DNS resolver issues.
What types of proxy servers are there?
There are many different types of proxy servers, all with different use cases:
Transparent Proxy
A transparent proxy tells the website it connects to that it is a proxy server. This transparent proxy also passes your real IP address along to the website, identifying you to the destination web server. The server host will thus see that you are connected via proxy, and know both your IP address and geolocation.
This type of proxy server is primarily used for content filtering in the workplace and at home. The transparent proxy provides the same internet experience as a direct connection thanks to sharing your real IP. Additionally, it can implement filtering rules to prevent access to not-safe-for-work (NSFW) websites.
This could be used in a school, office, or at home for parental controls on your children's devices. For enterprises, blocking access to Facebook, YouTube, and other sites can increase productivity and reduce bandwidth utilisation. This bandwidth usage reduction will improve local area network (LAN) and wireless area network (WAN) speed and reliability, further increasing productivity.
Anonymous Proxy
Much like a transparent proxy, an anonymous proxy will tell the website it connects to that it is a proxy server. Unlike transparent proxies, however, an anonymous proxy will obfuscate your IP address. This means that your IP address is hidden to the hosting server, preventing the website from viewing your IP geolocation.
Advertising content online is targeted based on your geolocation. By obfuscating your IP address through anonymous proxy servers, you could potentially prevent targeted ads from reaching your device, thus protecting your browsing privacy.
Anonymous proxy servers can either be protocol-specific (HTTPS only, BitTorrent only, and so on), or universal with protocol-independent proxies. Protocol-independent proxies require a tunnel, in similar fashion to a virtual private network (VPN). Protocol-specific proxies cannot be tunnelled, as only specific data packets are anonymised in this case.
Distorting Proxy
A distorting proxy functions in a very similar fashion to an anonymous proxy. The main difference here is your IP address is not obfuscated – it is distorted. This means you can trick websites into thinking you are in a different geolocation, despite the reality.
This type of proxy server is typically used to bypass geo-restrictions on web content. As an example, Netflix has a different service catalogue in the UK vs the USA. If you wanted to view this US-based content, you could connect to a distorting proxy in the USA and trick Netflix into thinking you are actually in the USA. Many websites have also implemented GDPR restrictions while they update their policies, meaning you can get around these GDPR-related content blocks with a distorting proxy.
High-Anonymity Proxy
The final proxy on this list is the high-anonymity proxy. These proxies are designed to maximise security and anonymity by rotating IP addresses on a single proxy server or even routing through multiple proxy servers across the world.
This type of proxy is used by the TOR Network, the delivery system for the fabled 'darknet' or 'deep web'. While TOR has connotations with black-market criminal activity, many websites on the darknet are legitimate and legal. These websites benefit from the highest possible levels of anonymity, thanks to the rotating IP addresses and multi-proxy routing we mentioned earlier. Rather than .com or .co.uk, TOR uses .onion, also known as ‘onion links’. This is due to the layered nature of TOR connections, much like an onion has layers!
The downside with multi-proxy routing is latency and page load times increasing. As the connection 'bunny hops' between proxies, you must wait for each proxy server to process and connect to another. The upside here is that each proxy server could be viewed as a potential originator for the connection, virtually eliminating the chance of tracking the data flowing through TOR.
As a test, we connected to fasthosts.co.uk using the Site24x7 Ping Tool. Our latency result from Toronto, Canada to the UK was 85ms. In comparison, TOR .onion connections (at 50KiB packet size) had a minimum of 2 seconds (2000ms) to request and download packets. The packet failure rate for .onion connections also sits between 0% and 12% depending on network conditions, reducing TOR's viability for latency-dependent applications.
Reverse Proxy
A reverse proxy server stands between web servers and the internet. It gets requests from clients like web browsers and sends them to the right web servers. This is different from a forward proxy, as instead, a reverse proxy works for the server, not the client.
When clients send requests, the reverse proxy passes them on to the backend server that can handle them. After the backend server deals with the request, the reverse proxy sends the answer back to the client.
Using a reverse proxy has many upsides for security, load balancing, and caching. It hides the identities and internal networks behind it, which keeps servers safe from direct internet traffic. This protects them from possible harmful attacks (such as DDoS).
For load balancing, the reverse proxy spreads incoming client requests among multiple servers. This stops any one server from getting too busy. It makes the system more reliable and cuts down on response times by managing traffic to give users a smooth experience. You may already be familiar with reverse proxies such as Apache!
Static Proxy
A static proxy is a kind of proxy server with a set IP address that stays the same. Unlike dynamic proxies, which might switch their IP addresses each time you use them or after a set time, static proxies keep the same IP address all the time. This steady IP address comes in handy for certain online jobs that need a reliable IP, such as running social media accounts, setting up online ads, or gathering data from websites.
This is an advantage, as many websites might flag or limit users who often change their IP addresses, as they see this as a possible security threat. But keep in mind that you need to handle online activities with care when you use static proxies. This helps avoid overuse or misuse that could get the static IP blacklisted.
What are the benefits of a proxy server?
Opting for a proxy server can benefit a few areas of your personal or business network. If you’re looking for better security, improved privacy and lots of other perks – a proxy server might be the right choice for you. Let’s run through some of the benefits:
1 - Control internet usage
If you’re wanting to block certain sites for employees or even your children, a proxy server can help. They can control internet usage and direct users away from certain sites – which is helpful for both businesses and parents.
2 - Improve security
A proxy server acts as a barrier between you and potential threats online by protecting your IP address. It is also possible to use encryption on a proxy server to ensure a secure connection. Or you could pair your proxy server with a VPN for extra security whilst browsing the web.
3 - Boost privacy
Browse privately by using a proxy server. This benefit pairs nicely with improving security, as using data encryption will prevent prying eyes from viewing your searches. Some proxy servers will change your IP address in order to protect your personal information and browsing habits.
4 - Performance improvements
Proxy servers have a handy feature of caching websites, and can check to see if they have the most recent version of a site before they send it over. This saves on bandwidth and helps to improve speeds.
What is a proxy server used for?
A proxy server stands between a user's device and the internet. People use it for different reasons. For example, it can speed up internet connections by storing web pages. It also boosts security by masking the user's IP address and coding data. Users can get around geo-blocks or internet censorship because it changes how their location looks.
Should a proxy server be on or off?
Keeping a proxy on helps protect privacy, makes online activities safer, and lets users see blocked content by hiding their real IP address. It can also speed up web browsing by storing data. But there are times when you might want to turn the proxy off, like when you need a quick direct link to the internet and don't need to stay anonymous.
How do I find my proxy server address?
To find your proxy server address on a Windows system, you can use the Command Prompt application.
First, you'll want to open the Command Prompt by pressing Windows Key + R, typing "cmd," and pressing Enter.
Inside the Command Prompt, typing "ipconfig" and pressing Enter will list your network configurations. Look for the "Proxy Server" or "Proxy" section to find the address next to the "Address" or "Server" field.
For macOS, you need to open the System Preferences, click on 'Network', select your network connection, and then click on 'Advanced.' Navigate to the 'Proxies' tab to find your proxy settings and address. Keep in mind that the names listed in these instructions for macOS may be labelled slightly differently, depending on the OS version you have installed.
What happens if you don't use a proxy server?
When you use the internet without a proxy server, your connection is more straightforward, but you lose the privacy advantage, as websites can see your actual IP address. Also, there's no built-in content filtering, which many businesses use to block certain sites. You might run into problems accessing content that's limited to specific regions or networks, which proxies can help you get around. You could also miss out on faster loading times from caching. There might be a higher security risk too, since proxy servers can give you an extra shield against harmful websites.
Proxy server hosting with Fasthosts
Proxy servers are an excellent way to protect your privacy and bypass geographical restrictions. You can create your own proxy server using our virtual private server (VPS) hosting services, and configure your server as you see fit. You get full, bare-metal access to server hardware, with complete freedom to install any OS or configure the server as you see fit. Unlimited network traffic makes this a viable proxy server option, and prices start from just £2 per month.